(Updated: August 21, 2023)
In December last year, Olaf Scholz succeeded Angela Merkel as chancellor of Germany. Since about half a year ago, he has a remarkably large red telephone at his desk, which appears to be the SINA Communicator H. This is a brand new device to conduct secure phone calls at different classification levels and part of the widely-used SINA architecture.
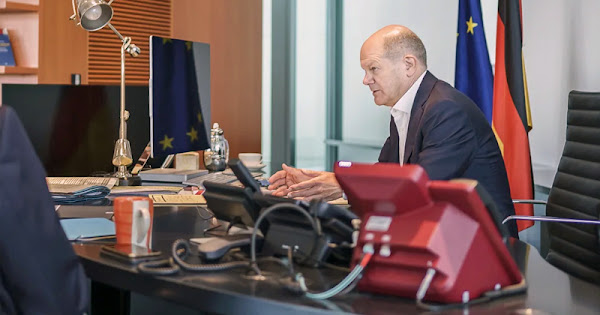
German chancellor Scholz with his new red telephone for secure calls
(photo: Jesco Denzel - click to enlarge)
(photo: Jesco Denzel - click to enlarge)
The chancellor's office
When the German government moved back to Berlin in 1999, a new Federal Chancellery was being built that was opened in May 2001 by chancellor Gerhard Schröder. Built in a postmodern style, it is said to be one of the world's largest government headquarters, with nine floors in the central part and over 300 offices in the wings.
On the 4th floor of the main building there's a room shielded against eavesdropping for meetings of the crisis staff (Krisenstab) and the weekly meeting of the heads of the secret services with the head of the chancellery (there's no bunker underneath the building).
The small situation room in the federal Chancellary (source)
with at least three Alcatel 4039 office telephones
with at least three Alcatel 4039 office telephones
Next to the secure conference room is a small situation room (Lage und Krisenzentrum) where information from all over the world is collected 24/7, a selection of which is put in a folder titled Nachrichtenlage which the chancellor finds on his desk every morning, similar to the President's Daily Brief for the American president.
The chancellor's office is on the 7th floor and is very spacious, with a seating area, a conference table and a large, almost 4 meter long black desk. Chancellor Merkel didn't like this desk and used it only for phone calls to foreign leaders. For her daily work she preferred the small conference table at the opposite end of the room.
> See also: How secure is the Merkel-Phone?
Various phones at the desk of chancellor Olaf Scholz (source)
Video impression of the chancellor's office (August 2023)
The chancellor's telephones
When Olaf Scholz took over the office from Angela Merkel in December 2021, he found two Alcatel 4039 telephone sets on his desk, one of them with an extension module providing 14 additional direct line buttons. The Alcatel 4039 is a high-end IP office phone with a tiny alphabetic keyboard as a distinctive feature.
Alcatel was the telecommunications branch of the French conglomerate Compagnie Générale d’Électricité (CGE), which in 1986 was merged with the telephone equipment part of ITT Corp. from the United States. This made Alcatel NV the world's second-largest telecommunications company. In Germany, Standard Elektrik Lorenz (SEL) had become an Alcatel subsidiary as well, with 20 percent of Germany's telephone equipment market in the early 1990s, second only to Siemens AG. In 2006, Alcatel merged with the American manufacturer Lucent Technologies to become Alcatel-Lucent, which was acquired in 2016 by the Finnish company Nokia and merged into their Nokia Networks division.
In an earlier video we saw that one of the phones had a red label and the other one a blue label. This likely indicates which phone is for classified conversations and which one for unclassified calls, according to the color codes of the German classification system:
- Blue: up to Confidential (VS Vertraulich)
- Red: Secret (Geheim) and Top Secret (Streng Geheim)
- Red: Secret (Geheim) and Top Secret (Streng Geheim)
Ultimately by February 2022, the Alcatel 4039 with the blue label had been replaced by a stylish new IP phone, the IP222, made by Innovaphone. This is interesting, because Innovaphone is just a small manufacturer, but as a German company its products may be considered less risky than those of foreign manufacturers.
The IP232 made by Innovaphone (click to enlarge)
The new red telephone
The first time the new red telephone on chancellor Scholz's desk was seen was during an interview with T-Online that was published on May 15, 2022. The phone got broader attention by a photo posted on Scholz's Instagram account on September 13, 2022, during or after a 90-minute phone call with Russian president Putin.
This was picked up by the German tabloid paper BILD, which in a video report (see below) suggested that Scholz had used his new red telephone ("back from the days of the Cold War") to make the phone call with Putin. However, on its website, BILD stated that for conversations with for example the Kremlin, Scholz uses another secure line.
The latter is most likely because for a secure phone line, both parties have to use the same encryption system, and in this case it's not very likely that the Germans would provide Putin with their newest secure voice encryption technology. In the United States, a "red phone" is also used for internal command and control communications and, despite widespread popular belief, not on the famous Hotline between Washington and Moscow.
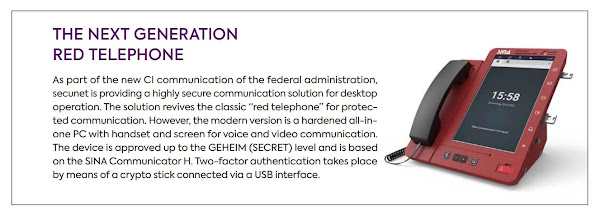
secunet Security Networks AG
BILD had also identified Scholz's new red telephone as the so-called SINA Communicator H. This device is manufactured by the German cybersecurity company secunet Security Networks AG, which is headquartered in Essen and was founded in 1997 as an offspring of the venerable testing association TÜV.
In 2004, secunet became a partner in the IT Security Partnership (Sicherheitspartnerschaft) with the federal Interior Ministry, which by then also included Rohde & Schwarz, Deutsche Telekom, Siemens, IBM Deutschland and Infineon.
Until recently, German government and military departments used voice encryption systems for ISDN, which was very popular in Germany. But German telecommunication providers are phasing out their ISDN service one by one, replacing it by Voice over IP (VoIP) via DSL. This made it urgent for the government to replace their existing voice encryption systems.
The SINA Communicator
Hence, secunet developed the SINA Communicator, for which it already had years of experience when it came to the hardware. For the necessary software for encrypted voice and video communications, secunet acquired the German company Stashcat GmbH, which in 2016 launched the Stashcat secure smartphone messenger that is used by some 50.000 German soldiers, as well as by schools, companies and local governments.
The name "SINA Communicator H" signifies that the device is part of the Secure Inter-Network Architecture (SINA) product family for securing digital data and communications (see below), in this case up to the classification level Secret. The latter is indicated by the letter H, as the last letter of the SINA product designations indicates their maximum classification level:
- S: up to VS-Nur für den Dienstgebrauch (Restricted)
- E: up to VS-Vertraulich (Confidential)
- H: up to Geheim (Secret)
- E: up to VS-Vertraulich (Confidential)
- H: up to Geheim (Secret)
As such, the SINA Communicator H was certified by the Federal Office for Information Security BSI in July 2021. Certification for organizations of the European Union and NATO has been requested.
The SINA Communicator is a fairly large and heavy device (weight ca. 5,5 kg) and despite the bulky look of its backside it won an iF Design Award earlier this year. Unlike common telephones, the SINA Communicator only has four buttons (for mute, up, down, and headset); all other functions are accessible through the 10,1" LCD touchscreen.
It seems that currently, the device can only be used for secure phone calls. A secure messenger, video telephony and the integration of thin client functionality will be part of future upgrades. Other options such as web clients, fax support, file and document transfer and multi-party messaging can also be added.
A special feature of the SINA Communicator is the Multi Level Data Separation, which means that users can communicate at different classification levels by selecting one of the approved levels via the touchscreen display. This will make it possible to use the same device to communicate with foreign partners as well.
The SINA Communicator supports up to three different networks, depending on the need of the user, which enable them to communicate at various German classification levels, or at (classified) networks of European and NATO partners, up to the level Secret.
For access to a particular network at a particular classification level, users get a hardware token in the form of a small key for each network they are authorized to. The key for each network has to be plugged into the phone to provide two-factor authentication:
The SINA Communicator can be used on dedicated government networks or directly on the public internet and is also compatible with the modernized command and control systems (Harmonisierung der Führungsinformationssysteme or HaFIS) of the German armed forces.
The Communicator uses standard VoIP protocols, including the Session Initiation Protocol (SIP) for common commercial systems and the Secure Communications Interoperability Protocol (SCIP) for secure communications with NATO partners.
Encryption is conducted with a "type A cryptographic suite" and key management through a Public Key Infrastructure (PKI) or the Internet Key Exchange version 2 (IKEv2), which can be upgraded to provide resistance against attacks by future quantum computers (PQC).
Update:
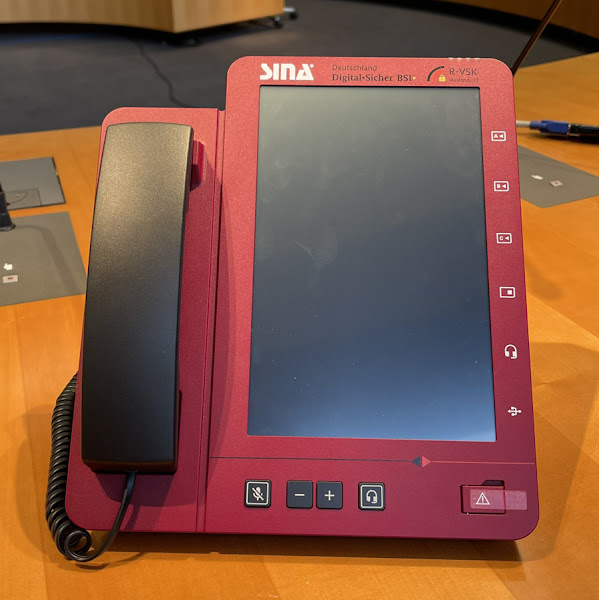
In October 2022, minister of state in the foreign office Tobias Lindner tweeted a high-resolution photo of the SINA Communicator in red, like the one on chancellor Scholz' desk (see below).
The photo shows that in the upper right corner the phone is marked with the abbreviation R-VSK, which stands for Ressortübergreifende Verschlusssachen-Kommunikation or in English: Interagency Classified Communication. This version is for use at federal government ministries and is currently being rolled out.
Next, foreign partners will be included (International, I-VSK) as well as companies where there's a need for secure communications with government agencies (Firmen, F-VSK). There are also plans to offer the system to German state governments (Länderbehörden).
To ensure its availability, the SINA Communicator is manufactured both by secunet and Rohde & Schwarz, the latter providing experience with secure communications for vehicles. The new phone system is also made redundant so it continues to function when there's a electricity blackout.
In October 2022, minister of state in the foreign office Tobias Lindner tweeted a high-resolution photo of the SINA Communicator in red, like the one on chancellor Scholz' desk (see below).
The photo shows that in the upper right corner the phone is marked with the abbreviation R-VSK, which stands for Ressortübergreifende Verschlusssachen-Kommunikation or in English: Interagency Classified Communication. This version is for use at federal government ministries and is currently being rolled out.
Next, foreign partners will be included (International, I-VSK) as well as companies where there's a need for secure communications with government agencies (Firmen, F-VSK). There are also plans to offer the system to German state governments (Länderbehörden).
To ensure its availability, the SINA Communicator is manufactured both by secunet and Rohde & Schwarz, the latter providing experience with secure communications for vehicles. The new phone system is also made redundant so it continues to function when there's a electricity blackout.
The SINA Communicator comes standard in black; the version in red seems to be for German government users to communicate up to the classification level Secret. It's not clear why this is signified with an almost completely red device, instead of with a less-eyecatching marking.
In the US, for example, the phones for calls at the highest level simply have a bright yellow bezel surrounding the display, but for the Oval Office apparently even that was standing out too much, so there the phone for secure calls looks almost identical to the one for regular phone calls, similar to the two Alcatel 4039 phones that had been on Scholz's desk.
The SINA architecture
The SINA Communicator is the latest addition to the Sichere Inter-Netzwerk Architektur or Secure Inter-Network Architecture (SINA) to protect classified information and communications. Following a tender by the BSI, secunet started developing the SINA architecture in 1999.
SINA enables the secure processing, storage, transmission and documentation of classified information and consists of a range of terminals and network encryption devices, including:
- SINA L2 Box: Encryption at OSI layer 2 with data throughput of up to 100 GBit/s.
- SINA L3 Box: IPSec encryption at OSI layer 3 with data throughput of up to 5 GBit/s.
- SINA Workstation: Providing secure access to both classified and unclassified networks.
- SINA Workflow: Dedicated document management system for classified information
SINA encryption
At the lower classification levels, message encryption was initially conducted via the classified cryptographic algorithm CHIASMUS, but this has been replaced with the publicly available AES block cipher. The SINA products also use the Elliptic-curve Diffie-Hellman (EC-DH) for key exchange and the Elliptic-curve German Digital Signature Algorithm (EC-GDSA).
At the higher classification levels, SINA products used the classified cryptographic algorithm LIBELLE, which was stored on the PLUTO crypto processor made by Infineon. This chip was integrated in a Hardware Security Module (HSM) called PEPP1, which was manufactured by Rohde & Schwarz. LIBELLE was gradually replaced by a new classified encryption algorithm.
Usage of SINA products
In Germany, SINA products are installed at goverment departments, military facilities, companies working with classified information and critical infrastructures. Also secured by SINA encryption devices are the wide-area networks for Secret information of the German foreign intelligence service BND, as well as the global secure network connecting German embassies via the internet.
Data that are intercepted under Germany's lawful interception authorities are also secured by SINA network encryptors when they are transferred from the telecommunications provider to the appropriate government agency.
SINA devices are also certified by the responsible authorities of NATO and the European Union and used by public institutions and commercial enterprises in other countries as well. Meanwhile, some 170,000 SINA products have been installed in over 30 countries.
In the Netherlands, for example, the cybersecurity company Fox-IT equips SINA boxes with its RedFox encryption module, which comes in a commercial version and one with classified algorithms for government users.
Links and Sources
- Tagesspiegel: Sicher über Geheimes reden (2022)
- secunet: SINA Communicator H factsheet
- BSI: SINA Broschüre (2016)
- BILD: Wenn beim Kanzler das rote Telefon klingelt (2022)
- Der Spiegel: Im Kanzleramt (2005)
- Verwaltungsvorschriften: Hinweise zur Handhabung von Verschlusssachen